Nuovi Use Cases e articoli
Link alle novità
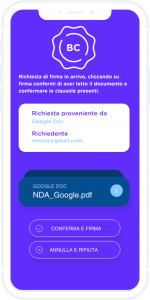
Signchain Signature
Firma elettronica Blockchain
La firma elettronica Blockchain eIDAS compliant: da remoto o in presenza. Perfetta per aziende, agenti e professionisti.
Contatta il nostro sales team

La firma elettronica Blockchain eIDAS compliant: da remoto o in presenza. Perfetta per aziende, agenti e professionisti.

Scytale è specializzata nello sviluppo di soluzioni di crittografia avanzata, firma elettronica ed autenticazione su protocollo blockchain.
Siamo nel settore della Blockchain da anni e in questo ambito è nata SignChain, piattaforma di firma elettronica avanzata basata su Blockchain conforme al regolamento eIDAS.
Questa piattaforma consente in modo univoco di associare un’identità crittografica a un set di chiavi private, salvate, sempre verificabili e trasparenti, su una Blockchain, appunto, terza parte fidata.
Il documento firmato con SignChain è come fosse stato firmato davanti a un notaio virtuale che garantisce la sua integrità, immodificabilità e dimostrabilità di essere certamente esistente nella data in cui è stato firmato.
In poche parole il documento è stato “notarizzato”.
Gli Smart Contract sono l’equivalente dei contratti tradizionali, tradotti in codice software e automatizzati: tutto ciò permette di verificare automaticamente determinate condizioni, auto-eseguire azioni o dare disposizione affinché si possano eseguire determinate azioni, nel momento in cui le condizioni determinate tra le parti sono state raggiunte e verificate.
Uno Smart Contract è basato su un codice che “legge” sia le clausole che sono state concordate, sia le condizioni operative nelle quali devono verificarsi le condizioni concordate e si auto-esegue automaticamente nel momento in cui i dati riferiti alle situazioni reali corrispondono ai dati riferiti alle condizioni e alle clausole concordate.
Rappresenta tutti i dati in formato elettronico, è la versione più semplice e utilizzata principalmente negli Stati Uniti e come segno grafico per le consegne dei corrieri.
Corrispondenza tra HASH su transazione BLOCKCHAIN e firmatario transazione (o credenziali di accesso al servizio)
Soluzione di firma che garantisce la connessione unica al firmatario, l'autenticità del firmatario e l'integrità del documento. Necessità di un contratto tra le parti.
Corrispondenza tra HASH su transazione BLOCKCHAIN e firmatario della transazione identificato con processo KYC
Soluzione di firma che garantisce la connessione unica al firmatario, l'autenticità del firmatario e l'integrità del documento. Necessità di un contratto tra le parti.
TO BE. BLOCKHCHAIN COME Certification Authority
La soluzione SighChain supporto la firma elettronica semplice e la firma elettronica avanzata. Ed è possibile firmare qualsiasi tipologia di documento o transazione.
Assicurazioni, aperture di conti correnti, privacy policy, richieste di mutuo, cessione del quinto.
DDT, ordini, acquisti, conferme di ricezione, bolle, passaggi di stato e certificazioni di processo.
Cosa rende uniche le notre soluzioni e cosa le differenzia da quelle adottate in predenza.
Sistema di autenticazione basato su chiavi proprie del dispositivo: ogni transazione è firmata, garantendo maggiore sicurezza e innovazione rispetto alle soluzioni basate su OTP.
La soluzione è integrata ed integrabile con sistemi di gestione documentale e di processo.

Ogni chiave pubblica utilizzata per una autenticazione è registrata nella blockchain. Se la stessa chiave viene presentata una seconda volta, viene rifiutata la richiesta di autenticazione ed emesso un evento condiviso con la rete. Condividendo la ricerca di manomissione sia a tutti gli utilizzatori del servizio, sia alle forze dell’ordine (polizia postale, finanza, etc).